A sophisticated Cyber attack recently observed by Venak Security demonstrated how threat actors exploited vulnerabilities in vsdatant.sys, a kernel-level driver used by Checkpoint’s ZoneAlarm antivirus software. Originally released in 2016, this driver became the target of a Bring Your Own Vulnerable Driver (BYOVD) attack, allowing attackers to elevate privileges and bypass critical Windows security features such as Memory Integrity and extract sensitive data from compromised systems.
As vsdatant.sys operates with high-level kernel privileges, attackers were able to exploit its vulnerabilities, bypassing security protections and antivirus software, and gaining full control of the infected machines.
Exploiting vsdatant.sys: Bypassing Memory Integrity
Windows’ Memory Integrity feature is designed to protect critical system processes by isolating them in a virtualized environment, making it harder for attackers to tamper with or inject malicious code.
Think of it like a security guard inside a locked booth. This isolated environment prevents the memory integrity feature from being tampered with by an attacker. A program that wants to run a piece of code which may be dangerous has to pass the code to memory integrity inside that virtual booth so that it can be verified.
However, the attack observed by Venak Security showed that a vulnerable driver, such as vsdatant.sys, could bypass this powerful defense.

The “Bring Your Own Vulnerable Driver” (BYOVD) technique has become a favored technique within Cyber Criminal groups to disable EDR products. This tactic involves bringing vulnerable drivers onto compromised systems and leveraging them to execute malicious code at the kernel level. By default, 64-bit versions of Windows 10 and later will load a kernel-mode driver only if the kernel can verify the driver signature. Hackers abuse digitally signed but vulnerable drivers by bringing them onto the systems and using them to terminate critical AV or EDR processes, enabling them to operate undetected in the compromised environment.
By exploiting flaws in vsdatant.sys, attackers were able to gain elevated privileges within the system’s kernel, effectively disabling Memory Integrity. Once these defenses were bypassed, attackers had full access to the underlying system, the attackers were able to access sensitive information such as user passwords and other stored credentials. This data was then exfiltrated, opening the door for further exploitation.
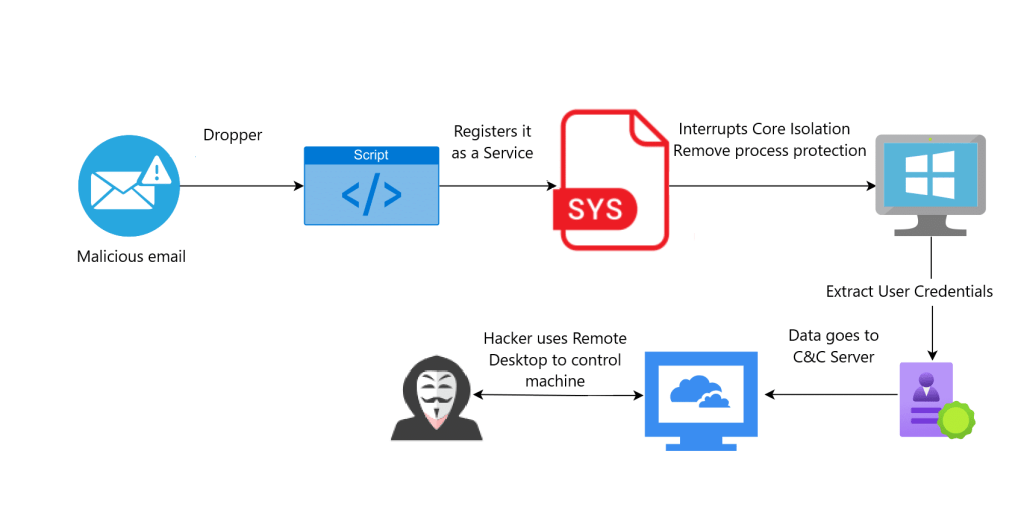
The attackers also established a Remote Desktop Protocol (RDP) connection to the infected systems, enabling them to maintain persistent access to the compromised machines.
During our investigation, we have noticed that since the device driver had a valid signature, our customer’s EDR ignored this attack and flagged it as safe.
Here is how this attack is implemented:
We were able to replicate the attack and show how hackers implemented it. Watch our video here:
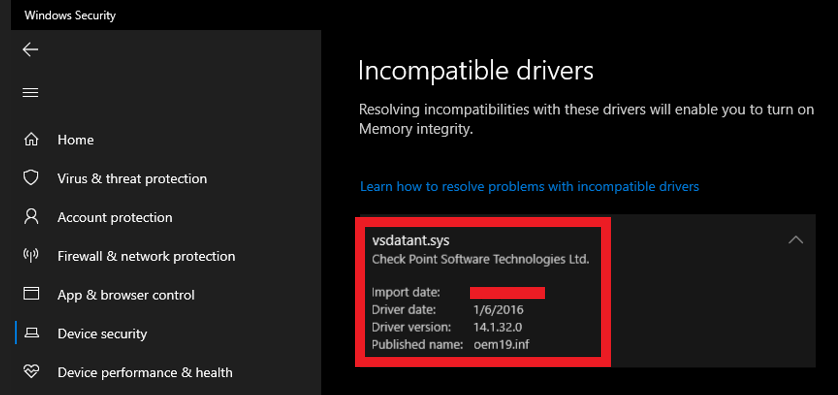
Vulnerable Driver Information
Name: Vsdatant.sys
Version: 14.1.32.0
MD5 Hash: 190fe0ce4d43ad8eed97aaa68827e2c6
The latest version of vsdatant.sys is not Vulnerable.
Summary:
The Vendor has already advised regarding this issue.
How can you prevent these types of attacks?
Contact us via email to request a free consultation.

Leave a Reply to Medusa Ransomware Uses Malicious Driver to Disable Anti-Malware with Stolen Certificates – SecuritydoneCancel reply