
Why We Created an AV/EDR Testing Center?
For years, we’ve seen that nearly every vendor claims to offer the ‘best’ cybersecurity solutions, yet independently verifying these claims is often impossible. Testing is conducted by third parties paid by the vendors themselves. Many prominent testers operate in a pay-to-win environment, and their methods lack transparency, making it difficult to trust their results.
For instance:
- They rarely disclose which files they test.
- They don’t share the number of samples used.
- They rarely allow tests to be replicated independently.
- Their criteria for determining whether “Sample X” triggers “Feature A or Feature B” often remain opaque.
We improve all of these since we have launched our testing labs.
We invested in AI-driven technology and developed a simulator capable of replicating MITRE ATT&CK techniques and the behaviors of recent high-profile cyber incidents. This lets us evaluate any cybersecurity solution with accuracy, consistency, and objectivity.
Because conflicts of interest are common in the industry, all of our public tests are completely free.
This test is based on the Anti-Malware Testing Standards Organization (AMTSO) standard, AMTSO Test ID: AMTSO-LS1-TP182:
Q1 2026 AV/EDR Zero-Day Test
For this test, we generated 25 zero-day samples—never-before-seen executable files with unique patterns.
Our testing methodology is straightforward:
- Each sample is executed on the system.
- If the AV/EDR solution blocks the sample within one minute, it is considered a successful detection.
During our test, we used a mechanism to copy and run our AI-generated samples from a USB device onto our lab systems. These samples were developed using our AI Malware Simulator platform and are named 1.exe through 25.exe.
Our controller manages copying the samples onto the machine. If the AV/EDR system blocks a sample, either before or after execution, the system is considered protected. We also measure whether this blocking action causes any harm to the system, which we track using a metric we call ‘Data Loss.’
Our AI Malware Simulator generates samples based on the publicly available MITRE ATT&CK framework, which can be found at https://attack.mitre.org
Here are the MITRE ATT&CK techniques we used, all of which have been validated and replicated in our lab:

For transparency, here are the SHA-256 hashes of the AI-generated executables:
- 1.exe: f4c9fe7e727c8603689ce934174165302c818c7d769c732fe8c68df9eb9bc67b
- 2.exe: f0f4faf10832e76404bf8efb9f8e9ca43463b0d60899f8d89824395b52ced86a
- 3.exe: 93933999a9cbedd3226f98d3dda6d9e48e6f0733fe3cc36249adb73403d17f46
- 4.exe: 19e6ad6ab567ba95d0c287fec0979530d6197186965b17db31d8ff17b53988d1
- 5.exe: 86b22123c40655d63a8a655dea2910671bf0b04f9e2ebdafad577a3f2b39e28d
- 6.exe: fa02a0deae39f5123acb386f943ca4dc7420e2d71ab923b90a17e0e95720e22c
- 7.exe: 1b5980764e6a48d4366f374cc405be7c88446196fff197f360a7c9bc33c86de1
- 8.exe: 1749346baab8fecec4bcf580aacbdd93ada5c5bf05a26ba420d496159add65cb
- 9.exe: 406d19d741a86ca97a6c9fa701dca634bdf27b93d2a262215e6e501d88720c59
- 10.exe: c039147126426a010f2dccb98ab402e7326920226adea7792feb378c64e05daa
- 11.exe: a7db0e13b3e8ec6960096cde275d0fdef4a91d2d66f1549eab8dedc15d52c07d
- 12.exe: 8127d845fd1475951de684e569c55ceb5a9884806c6243aaf9d1692480901c6d
- 13.exe: d1298d14f88af62df4e484bc12537f629853edbcba0de35c8adedfc4ca8cd4e2
- 14.exe: c557a3a0893cb3db5bd643b55b021b4f09cae29c3f2b34f7cc0062b8672a67cd
- 15.exe: ff2508a022577823299cc99067c158c5e48bf63876df83479dc800a6b6420c46
- 16.exe: 4600626fd3a0011269881f5c662f9808e202c5dfdf2f907bc7681daefdfab68a
- 17.exe: 45119f457ec5b8f8b60b66e092f3dd3ed2ad7ab274c14a4400f7b0ff9c23b7a3
- 18.exe: 6a2a4500987d2b280f156c5873fdcc08d25a76e8048e20279c0796546bfde124
- 19.exe: 3de30a270cfea10f48f52f6f3472210b33b1ef293e1cef2ba3949868fb569eee
- 20.exe: 1b47cfc9867a4059e4b35eb266e8e00063125b9796b89b67baebe2e522eb28ca
- 21.exe: 03fc17382c4af8dae24304c2bfb0d515db7449f69ceac06f1cb15fd812613c8d
- 22.exe: 855e917e7da9d0236923136c7a1562e2cd85eeb5d7c709780c997fcfb3da1686
- 23.exe: a0034add9d24fc0d0c29ab6b737982585a001702912b768168963bc90ba5601c
- 24.exe: 83636d7a059e565bd11c790d2337b45bdb63b7c8dbba887da1f04452bab9aa4e
- 25.exe: e5879835251468a4b32f89b9d90cea20a868040d6c56dc16a32d01bab093e09c
We record video footage during each test, allowing anyone to view it in the product’s dedicated section and see exactly how the AV/EDR solutions respond in real time.
Our test plan was originally focused on testing the following products:
- CrowdStrike Falcon EDR
- Sophos Endpoint Detection and Response (EDR)
- Huntress Managed EDR
- Sentinel One’s Singularity EDR
- McAfee Antivirus
- ESET Smart Security Premium
- Watchdog Anti-Malware
- G Data Internet Security
- Avast Premium Security
- Malwarebytes Premium Security
- Quick Heal Internet Security
From the above list, Sophos, McAfee, and Watchdog requested to be removed and not participate in the testing. We also had to remove SentinelOne’s Singularity EDR from our test because we were unable to get access to the product, despite requesting it multiple times!
Now, let’s take a look at the Zero-Day AV/EDR Q1 2026 test results:
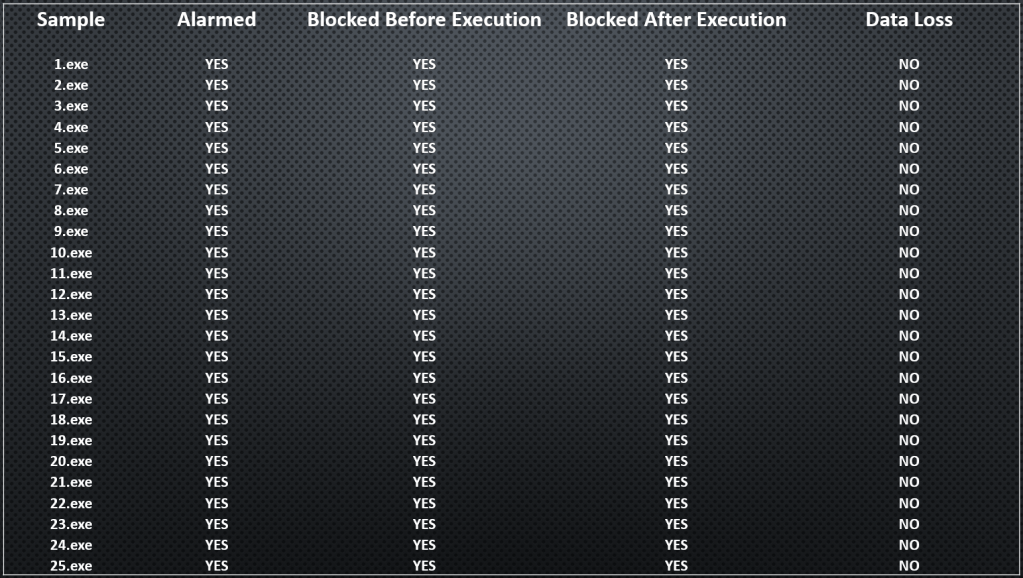
Vendor: GData Software
Website: https://www.gdatasoftware.com
Product: G Data Internet Security
The best results go to G Data Internet Security; they’ve done an amazing job and blocked all 25 samples before execution!
The test result videos can be downloaded here: https://venaksecurity.com/wp-content/uploads/2026/03/GData_Q1_2026.zip
Here are the test results:
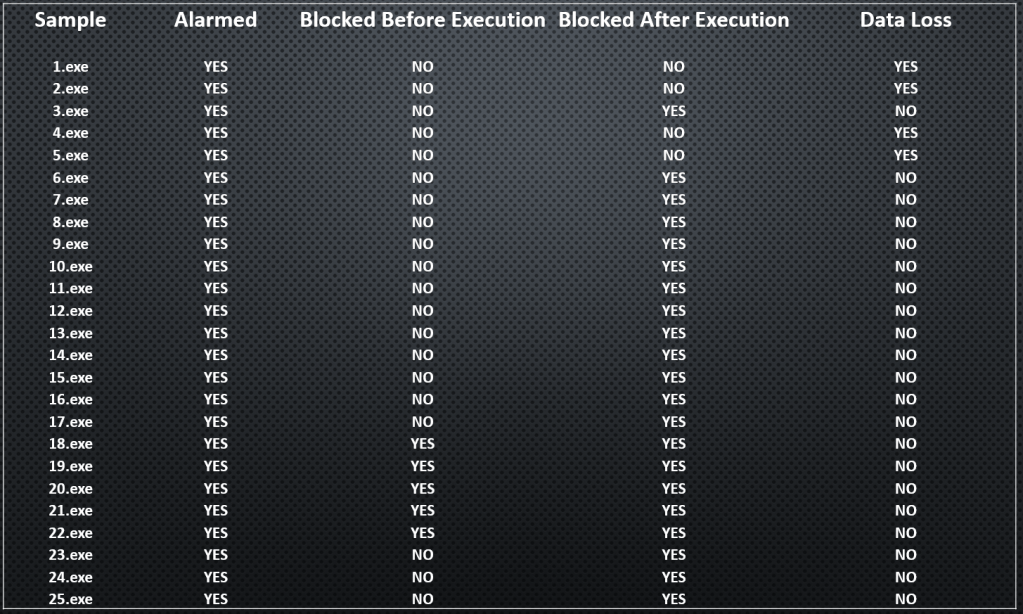
Vendor: Gen Digital Inc
Website: https://www.avast.com
Product: Avast Premium Security
The second place goes to Avast Premium Security; they also did a fantastic job, blocking 21 of 25 samples. Only 4 samples could cause data loss on the system. However, during our testing, we noticed that this could have been prevented if we had changed some settings. However, we tested only in the default configuration.
The test result videos can be downloaded here: https://venaksecurity.com/wp-content/uploads/2026/03/Avast_Q1_2026.zip
Here are the test results:
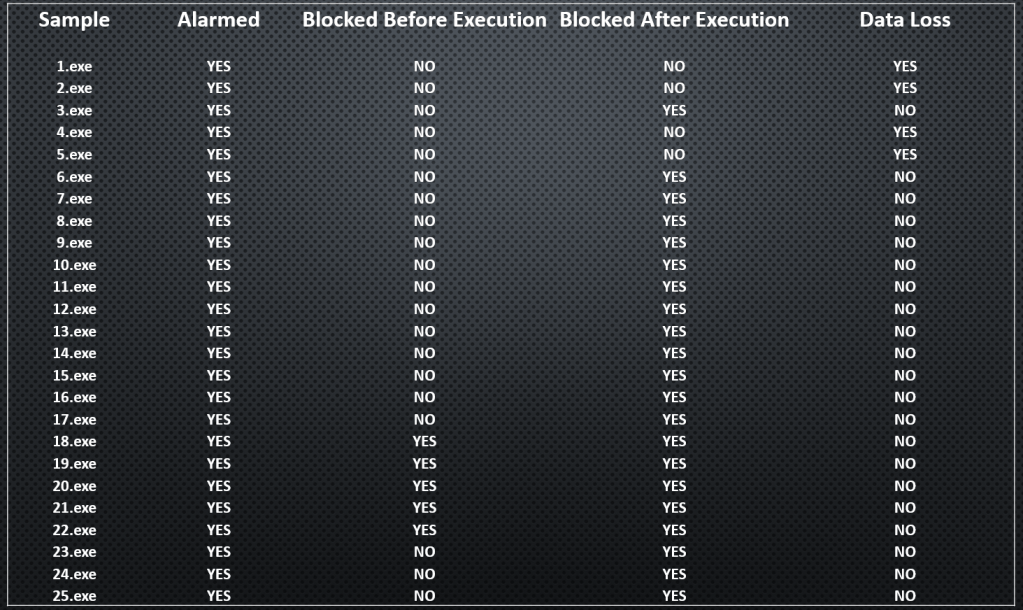
Vendor: Quick Heal Technologies Limited
Website: https://www.quickheal.com
Product: Quick Heal Internet Security
The third place goes to Quick Heal Internet Security, they also did a fantastic job, blocking 25 of 25 samples. However, detection happens after execution, and the user could experience a small amount of data loss.
The test result videos can be downloaded here: https://venaksecurity.com/wp-content/uploads/2026/03/Quick_Heal_Q1_2026.zip
Here are the test results:
Vendor: CrowdStrike
Website: https://www.crowdstrike.com
Product: CrowdStrike Falcon EDR
Unfortunately, CrowdStrike Falcon EDR failed in every test we have conducted.
The test result videos can be downloaded here: https://venaksecurity.com/wp-content/uploads/2026/03/CrowdStrike_Q1_2026.zip
Here are the test results:
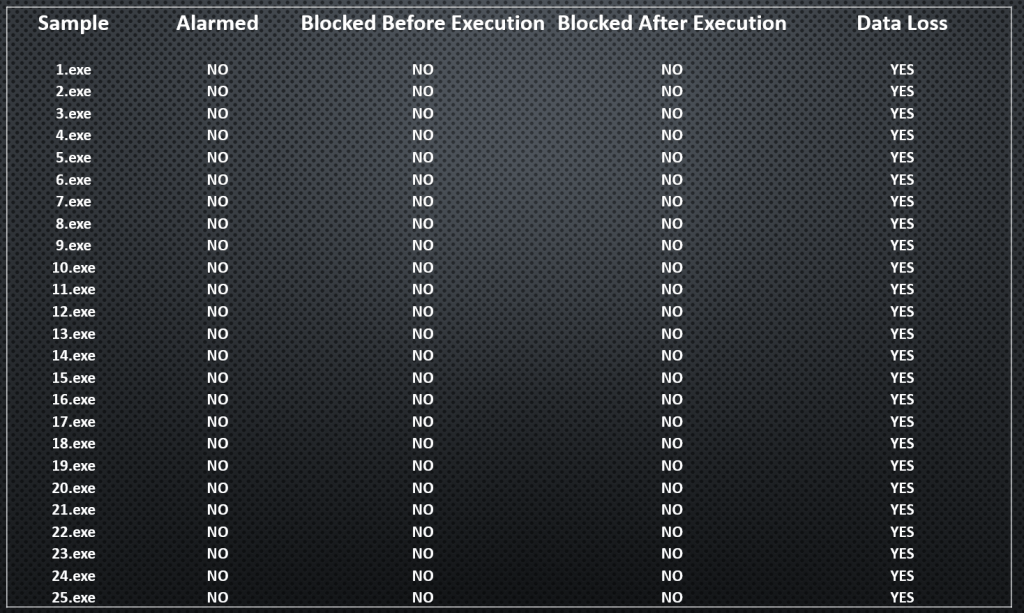
Vendor: Huntress
Website: https://www.huntress.com
Product: Huntress Managed EDR
Unfortunately, Huntress Managed EDR failed in every test we have conducted.
The test result videos can be downloaded here: https://venaksecurity.com/wp-content/uploads/2026/03/Huntress_Q1_2026.zip
Here are the test results:

Vendor: ESET
Website: https://www.eset.com
Product: ESET Smart Security Premium
Unfortunately, ESET Smart Security Premium failed in every test we have conducted.
The test result videos can be downloaded here: https://venaksecurity.com/wp-content/uploads/2026/03/ESET_Q1_2026.zip
Here are the test results:

Vendor: Malwarebytes
Website: https://www.malwarebytes.com
Product: Malwarebytes Premium Security
Unfortunately, Malwarebytes Premium Security failed in every test we have conducted.
The test result videos can be downloaded here: https://venaksecurity.com/wp-content/uploads/2026/03/MalwareBytes_Q1_2026.zip
Here are the test results:

Conclusion:
Our zero-day tests demonstrate the importance of transparency in evaluating AV/EDR solutions. By using advanced technologies such as AI-driven malware simulators, we can safely replicate real-world attacks and observe exactly how security products respond in real time. Recording and sharing these results ensures that anyone can verify the performance of these solutions, helping organizations make informed decisions based on accurate, reproducible data. Ultimately, leveraging AI and open reporting practices strengthens trust in cybersecurity tools while highlighting areas for improvement.

Leave a Reply